The Microsoft Defender for IoT research team has detected a cross-platform botnet designed to infect Windows, Linux, and IoT devices. The botnet dubbed “MCCrash” then launches distributed denial of service (DDoS) attacks against private Minecraft servers.
The team spotted the botnet originating from malicious software downloads and tracks the cluster of activity as DEV-1028.
“Our analysis of the DDoS botnet revealed functionalities specifically designed to target private Minecraft Java servers using crafted packets, most likely as a service sold on forums or darknet sites,” Microsoft wrote in a blog post.
Moreover, Microsoft said the botnet can spread by enumerating default credentials on internet-facing systems insecurely configured with open SSH ports for remote access.
“The botnet’s spreading mechanism makes it a unique threat, because while the malware can be removed from the infected source PC, it could persist on unmanaged IoT devices in the network and continue to operate as part of the botnet,” Microsoft added.
Most of the targeted devices appear to be in Russia as well.
DDoS botnet workflow
According to Microsoft, the DDoS botnet attack flow originates when a user downloads a malicious cracking tool or other malicious software onto the system. The tool then proceeds to download and launch a fake version of svchost.exe (such as ‘svchosts.exe’) through a PowerShell command (as noted in Figure 1).
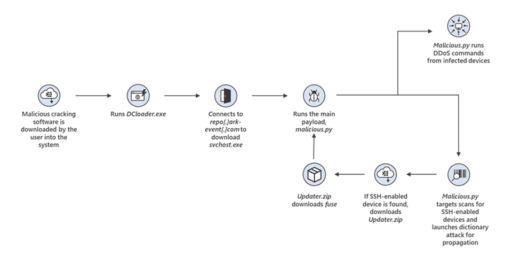
Next, the main Python script (malicious.py) runs and scans the internet for SSH-enabled Linux-based devices to then launch a dictionary attack to propagate the botnet.
The infected devices are then used to launch DDoS attacks against private Minecraft servers using known server DDoS commands and unique Minecraft commands.
In conclusion, Microsoft also provided additional guidelines and details regarding recommended remediations, indicators of compromise (IoC), and malware detections on the botnet threat.
Related Articles
- XorDdos: DDoS malware targets Linux systems
- Zerobot botnet exploits 21 vulnerabilities to breach targets
- Mirai variant MooBot botnet targets multiple D-Link flaws
- Emotet botnet reemerges with new threat behaviors
- Agenda Ransomware gang uses Rust to target more companies worldwide
- ‘Achilles’ vulnerability exploit bypasses macOS Gatekeeper